The difference between AWS regions, availability zones and edge locations
Regions, availability zones and data centres are all part of the AWS global infrastructure. They are physical units of the AWS ecosystem in a well-defined geographical area.
On the other hand, VPC and subnets are logical units, although they also have some geographical restrictions.
Let’s quickly see the difference between them.
Regions
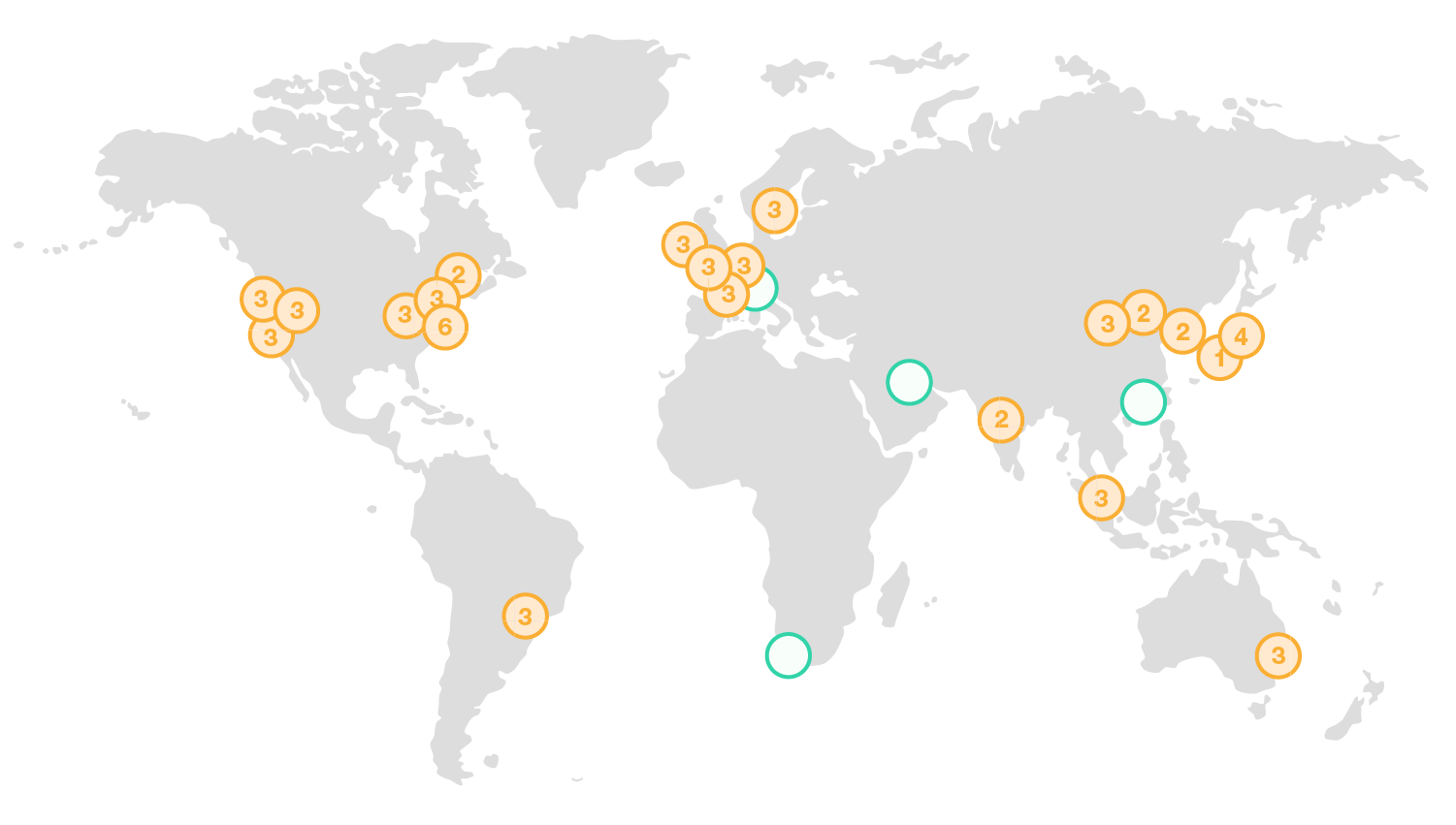
Regions are geographic locations and they can be found on all continents in the world. As of writing this, AWS has 20 available regions, and they keep expanding. Chances are that by the time you read this, they will have more than that.
Regions, as being separate locations, are physically isolated from each other. By having regions in all segment on the world, AWS managed to achieve high fault tolerance and stability in their services.
Mission critical applications can be backed up between multiple regions through the internet, or, since 2017, accounts can use AWS’s private network to connect to other regions.
Examples for regions are North-Virginia, California, Frankfurt or Sydney. Some regions like the AWS GovCloud regions are not available for new accounts.
Resources are region specific
As regions are well separated from each other, services are region specific. When an account is created, AWS creates a VPC (Virtual Private Cloud) and its basic elements in each region for the account.
If I run an application in the Sydney region, I can only look at the instances, routes etc. in that region. If I select another region like Frankfurt in the AWS console, I won’t see the instances from the Sydney region. Instead, the instances of the Frankfurt region will be visible, if I have launched any in that region.
Availability zones
Each region has at least two availability zones, which are physically separated units within the region. The only exception is the Asia Pacific (Osaka) local region, which has only one availability zone at the moment.
Availability zones are connected to each other by AWS to provide redundancy and low latency, so the communication between availability zones in the same region occurs on AWS’s private network.
By default, when an instance (EC2) like a web server is launched, we can select the availability zone or let AWS do this for us. It’s a good idea to let AWS select the availability zone because they know better which availability zone has more capacity to host our application. AWS strive for even distribution between the availability zones and the best one will be picked during the launch of the instance.
For the same reason, it’s possible that not all availability zones can be selected. Some of them might not even be offered for new accounts, so the best is to let AWS select the right zone for us.
As stated above, availability zones are located in different places in the same region, i.e. they are physically isolated. To increase availability and redundancy, we can decide to expand our application to have elements in multiple availability zones. If the architecture is properly designed, unexpected and unlikely events in an availability zone (flood, fire etc.) won’t make the application unavailable, and it can continue to operate without disruption.
Data centres
An availability zone can have one or more highly secure data centres. Data centres are the physical buildings or rooms where the high performance machines connected with cables and cords can be found.
Edge locations
Of course, as it can be seen from the picture above, not all segment of the world falls close to an AWS region, although AWS continually expands the list of regions.
To improve service and provide low latency, AWS has edge locations around the world that are used with their CloudFront service.
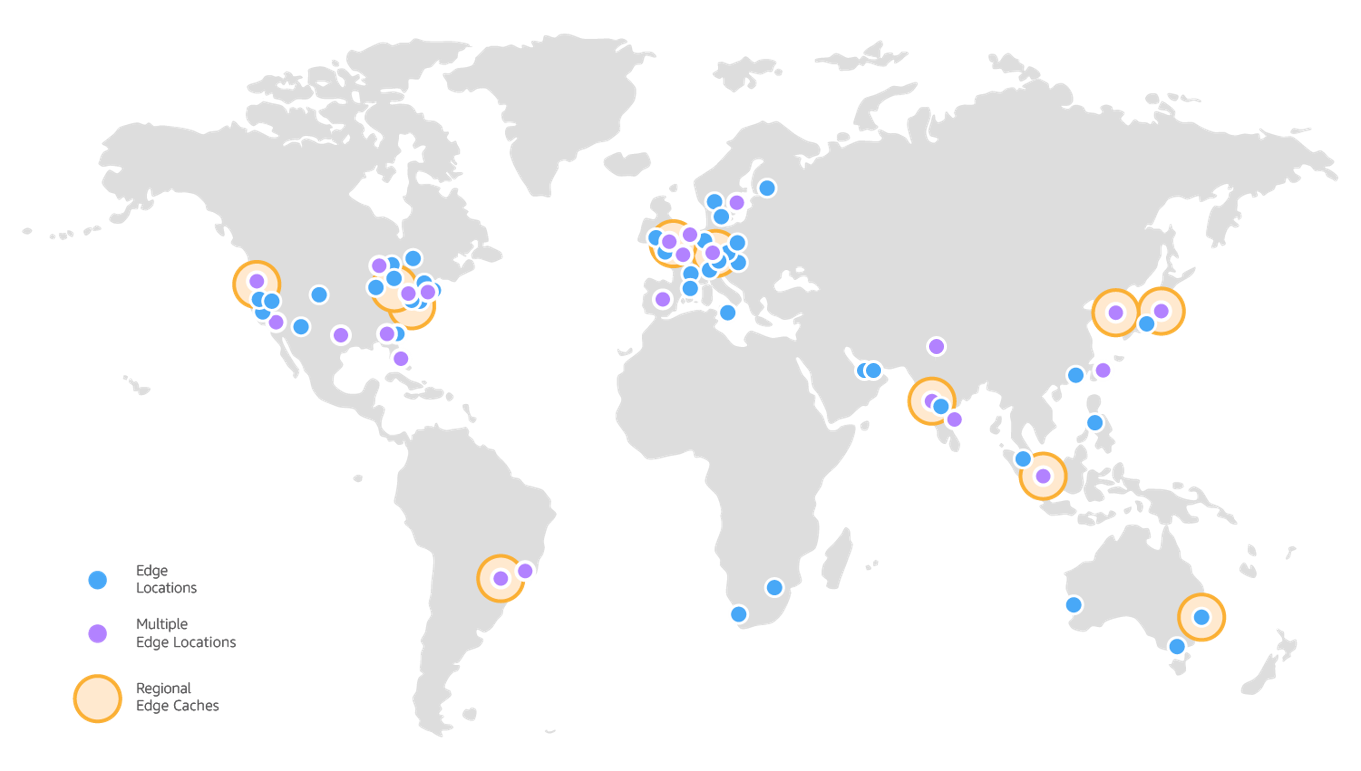
The network of edge locations are used to cache static and dynamic contents of our application and this content is distributed by CloudFront.
When users access the application, they will be served the cached version by the nearest edge location. If the content is already at the location where the lowest latency can be produced, it will be delivered to the user.
If the content is not available at the edge location that provides the lowest latency, it will be pulled from the service where the content is stored. Where the user requests the content, it will be routed from the origin to the relevant edge location through AWS’s network and it’s stored in the cache.
VPC (Virtual Private Cloud)
We have arrived to the world of the logical units. Although it can be physically isolated if created on a separate machine, a VPC is a logical, virtual network, which is dedicated to one account and is isolated from other VPC’s.
A VPC is like a traditional network that consists of routers, firewalls and servers, but they are all virtual devices. VPC’s are logically separated from each other and company A can’t have access to company B’s VPC network, just like their network devices were physically separated a decade or two ago.
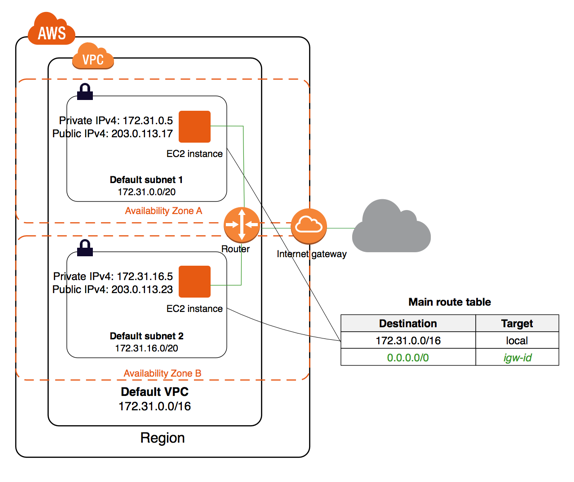
VPC’s are restricted to one region, and they can’t span multiple regions, but they span the availability zones in the region.
VPC’s have their own IP address range, within which their elements communicate with each other, and they access the internet through a virtual device called internet gateway.
Subnet
Subnets are parts of the VPC and they get a slice from the IP address range the VPC has. They are therefore smaller units, where the instances like a web server or a database server can be launched.
Subnets are confined to one availability zone and they can’t span multiple availability zones. But, of course, subnets in different availability zones can talk to each other, because they are within the same VPC.
Here’s a diagram on a VPC and its subnets. It shows one VPC in a region with two availability zones, and both availability zones contain one subnet each.
Note that VPC’s can also communicate with each other but this is beyond the scope of this post.
Conclusion
AWS’s large network is located in various geographic locations across the world. The main elements of the network are the regions, availability zones and edge locations.
Within each region, customers can create their own virtual network called Virtual Private Cloud or VPC. VPC’s replace the traditional physical network devices in the cloud. VPC’s contain multiple subnets, one in each availability zone by default. The subnets can communicate with each other within the VPC because they are assigned a slice of the VPC’s private IP address range.
Thanks for reading this post, and see you next week.